Essential Strategies for Securing Your Data in the Cloud
In today’s digital age, ensuring the security of your data in the cloud is paramount. Imagine losing all your vital information overnight—it’s a nightmare scenario for anyone. But don’t worry; by implementing a few essential strategies, you can safeguard your data and sleep peacefully knowing your information is secure.

Understanding Cloud Data Security
You might be wondering, “Why is cloud data security so important?” Well, the cloud offers unparalleled convenience and efficiency, but it also comes with its share of vulnerabilities. Cyberattacks, data breaches, and unauthorized access are just a few risks. Therefore, implementing strong security measures is not just a good practice—it’s a necessity.
1. Data Encryption
Encryption is the process of converting your data into a code to prevent unauthorized access. When your data is encrypted, even if a hacker gets hold of it, they can’t read it without the decryption key. Always ensure your data is encrypted both at rest (when stored) and in transit (when moving). Learn more about encryption.
2. Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) adds an extra layer of security. Instead of just a password, MFA requires additional verification, such as a text message code or a fingerprint scan. This significantly reduces the chances of unauthorized access. More about MFA.
3. Access Controls
Implementing Access Controls means giving permissions only to those who need it. Use Role-Based Access Control (RBAC) to ensure that users have access only to the data they need to perform their jobs. Always follow the principle of least privilege. Explore RBAC.
4. Regular Security Audits
Conducting Regular Security Audits helps you identify and fix vulnerabilities. Use tools to continuously monitor your cloud environment and keep track of any suspicious activities. Regular audits ensure that your security measures are up-to-date and effective. Importance of security audits.
5. Data Backup and Recovery
Always have a Data Backup and Recovery plan in place. Regularly back up your data and ensure that you can quickly restore it in case of a breach or data loss. This minimizes downtime and helps maintain business continuity. Backup strategies.
6. Use of Secure APIs
APIs are gateways to your data. Ensure you are using Secure APIs to prevent unauthorized access and protect data integrity. Regularly update and patch your APIs to close any security loopholes. Securing APIs.
7. Compliance and Regulatory Requirements
Stay compliant with regulations such as GDPR, HIPAA, and others. Ensuring Compliance not only protects your data but also saves you from legal troubles and hefty fines. Regularly review compliance requirements and update your security practices accordingly. Understanding compliance.
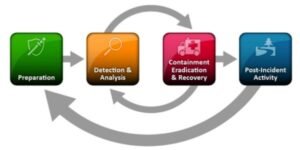
8. Security Incident Response Plan
Be prepared with a Security Incident Response Plan. Know what to do in case of a security breach. Your plan should include steps for identifying the breach, containing the damage, and recovering data. Regularly test your incident response plan to ensure effectiveness. More about incident response.
9. Employee Training and Awareness
Employee Training and Awareness are crucial. Educate your staff about security best practices and the importance of following them. Regular training sessions help keep everyone informed about the latest security threats and how to avoid them. Training tips.
10. Utilizing Security Tools and Services
Take advantage of Security Tools and Services such as Cloud Security Posture Management (CSPM) and Security Information and Event Management (SIEM). These tools help in monitoring, managing, and enhancing your cloud security. Security tools overview.
Components of Data Security in Cloud Computing
To wrap up, it’s essential to understand the five components of data security in cloud computing:
- Confidentiality: Protecting data from unauthorized access.
- Integrity: Ensuring data is accurate and unaltered.
- Availability: Ensuring data is accessible when needed.
- Accountability: Tracking who accesses data and when.
- Non-repudiation: Ensuring data authenticity and proof of origin.
Conclusion
Securing your data in the cloud might seem daunting, but by following these essential strategies, you can significantly reduce the risks. Stay vigilant, keep updating your security measures, and educate your team. Remember, the security of your data is in your hands. Read more –
